Distributed Denial of Service attacks, or DDoS, have become a widespread phenomenon and a serious problem for owners of websites, applications and online resources around the world. For those who want to avoid downtime, huge losses and a damaged reputation, DDoS protection is no longer an option, but a necessity.
In this article, we will describe what DDoS is and how to protect your online resources.
How does a DDoS attack work?
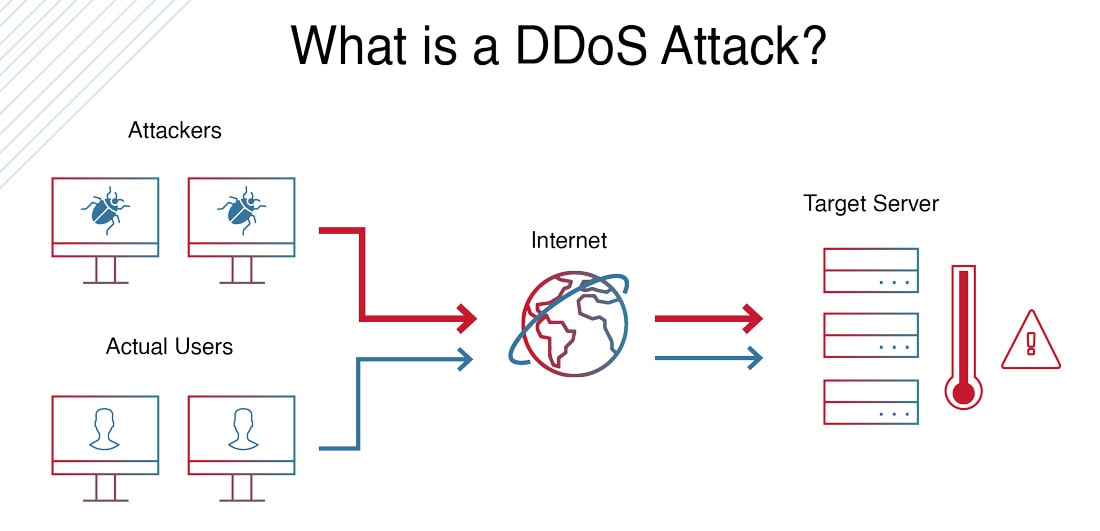
Distributed Denial of Service is attacking an information system to make it unable to respond to user requests. The point of the attack is to overload a web resource or server with traffic from many sources, making them unavailable. Often such an attack is carried out to disrupt the network resources of a large company or government organization.
DDoS resembles another common web threat, DoS. The only difference is that a typical distributed attack comes from a single source, whereas a DDoS is more widespread and comes from a number of different sources.
In the case of a DoS, it works like this:
-
The attacker sends many requests to the server; at the same time, normal users also send their normal requests;
-
Since the server's capacity is limited, it puts both normal and malicious requests in a long queue;
-
The server responds either very slowly or not at all;
-
As a result, online services do not work.
Reasons behind a DDoS attack
Besides making services inaccessible to visitors, DDoS is used to distract from other malicious effects. For example, to hack into a security system and steal an organization’s database.
If the target of a DDoS attack is an Internet root server, CDN provider or DNS server, the entire Internet can experience the consequences: most sites slow down or stop responding. Attackers use this to replace the real site with a fake one and use it to steal user data.
In 2012, CDN provider CloudFlare was the target of a 65 gigabit per second attack. At the time, the company was unable to cope with such a load. As a result, users experienced slow internet speeds for several days, because the global cache that speeds up content downloads was not working.
How to identify a DDoS attack
When the attacks reach their targets, they can be detected immediately by outages. However, there are a number of indirect signs, which can help you spot a DDoS attack in its early stages.
-
Server software and operating systems start to hang, terminate incorrectly, etc.
-
A dramatically increased load on the server's hardware, which is very different from the average daily performance.
-
A rapid increase in incoming traffic on one or more ports.
-
Multiple duplicates of a single type of client action on a resource (visiting a site, downloading a file).
-
Analysis of server, firewall or network device logs reveals many requests of the same type from different sources to the same port or service. You should be particularly suspicious if the list of requests is dramatically different from the target audience for the site or service.
How to prevent DDoS attacks
To avoid the unpleasant consequences of attacks and to protect your website, you should be aware of the methods of prevention and protection against attacks.
Preventing DDoS attacks:
-
Set limits on the speed and number of connections per IP address.
-
Use advanced firewalls and IDS/IPS systems to detect and block suspicious traffic.
-
Use CND. Content Delivery Networks (CDNs) help distribute traffic across multiple servers, reducing the risk of attack.
-
Use anti-DDoS services to filter out malicious traffic.
-
In the event of an attack, set up additional communication channels to keep resources available.
-
Update software regularly to address vulnerabilities that could be exploited in an attack.
-
Monitor activity on your site or server to quickly identify anomalies.
-
Provide security training to employees so they can respond quickly to incidents.
It is important to remember that DDos can cripple even the most secure web resources. This can result in huge losses, loss of customers, and damage to reputation. That is why it is an urgent task for all commercial organizations and government agencies to protect their resources from DDoS attacks.
Among other things, it is always important to have fresh backups just in case, so that you can quickly move to a new server or recover lost data.



